| © 2022 Black Swan Telecom Journal | • | protecting and growing a robust communications business | • a service of | |
| Email a colleague |
October 2012
Clever Integration: The Sherlock Holmes Way to Tease Solutions from a Fog of Misaligned Data

Big Data? Forgive me for being cynical, but these days I’m suspicious of any noun with the “Big” adjective in front of it.
“Big” things often lead to big disappointments: Big Banks, Big Government, Big Debt, “Too Big to Fail” automobile companies, and “Big Transformation” projects that cost a ton of money but fail to make a telecom’s operating environment simpler or less costly to maintain.
If it was my choice, I’d substitute “Big Data” with something a little more descriptive like “Real-Time Data” or “Fine-Grained Data”? In analytics terms, those are the chief benefits you get from these cheaper and faster boxes: the chance to act on data quicker and view it in far greater detail.
Now while Big Data enables many new capabilities, its value is greatly enhanced when you can combine it with “Big Thinking”.
Big Thinking is what Benedict Enweani and his UK-based software firm Ontology are all about. And we’re pleased that Benedict has agreed to be interviewed in Black Swan.
First off, I must warn you to not be intimidated by that obscure word, “ontology”. Not to worry. Benedict does a great job of explaining his firm’s technology here. The Ontology guys are brainy, down-to-earth people, not philosophy professors tossing $10 words around to put you to sleep.
I’m not going to steal Benedict’s thunder, but I will say that the analogy to Sherlock Holmes style thinking is very apropos. You can apply deductive reasoning to investigate anything from mysterious murders to complex telecom systems.
As opposed to attacking integration issues with an army of Scotland Yard investigators though, Ontology uses a clever, repeatable method to orchestrate solutions at relatively low cost. My hunch is you can apply this stuff to many business assurance problems.
| Benedict, it would be great if you explained the origins of your firm. |
Sure, Dan. So, the genesis of Ontology, myself and my co-founder, Leo Zancani worked together at Orchestream, a mid-90s startup that focused on IP, VPNs, and internet services provisioning. Orchestream was acquired in 2003 by Metasolv, then soon after by Oracle.
And the thing we noticed in each and every deployment was it would take 8 out of 10 days to align data coming out of billing, CRM, and inventory systems so that we could just create the IP VPNs for the customers and put them on to the network.
This data alignment issue wasn‘t simply an Orchestream problem. In fact, every single deployment a service provider makes raised this issue. And the problem stretches from the Tier 1 giants to very small operators. BT, for instance, has about 3,000 different OSS systems for their core operations and even small service providers and ISPs have 10 to 20 different systems.
If you have a large array of clean systems, traditional integration technologies can actually bring data together quite nicely. Likewise, if you only have a few systems and the data is dirty, you can manually clean up those systems and get a joined up view of your customers, bills, and equipment at relatively little cost.
But here’s the point: whether you have 10 systems with very dirty data or 100 systems with moderately dirty data, there is not a single technical solution you can turn to that will bring those data together because the many misalignments are so hard to pin down.
And in many cases, the inventory and CRM suppliers are more than happy to take on these data cleanup projects. Some get rich from that type of work.
| Wouldn‘t it be nice if telecoms were like Amazon.com where it is like one-to-one relationship between a book sold and something in physical inventory? In telecom, things are never that simple. |
Exactly, we’re now helping Level 3 Communications to align their inventory and CRM. At face value, it sounds rather straightforward, but the problem is very complicated because there are something like 12 different systems where inventory data is stored.
The other complication we have in the telecom industry is that different internal consumers of data look at it in entirely different ways. In service provisioning, it’s about configuring ports on a Cisco router. In a Siebel CRM, you focus on a catalog of products with certain customer-restricted parameters. In a billing system, you worry about a line item associated with a particular customer order. In a performance management system, you’re collecting events and matching that with a service model and IP addresses.
| So how do you begin to address this immense complexity? How do you decide where to even start? |
Well, suppose we wanted somebody with a fresh perspective to come in and solve the problem. What if we went to the owner of a Mom and Pop shoe store and said, “Here’s our network operations center. It’s a mess and I want you to go fix it.”
Five days later, the guy from the Mom and Pop store returns and says, “Yeah, I fixed it.” And you stand there incredulous and ask him what he did and he says:
“I started with the network and saw where the actual services were and wrote those down. Then I went to the CRM system to look at the ”adds“ and ”deletes“ to determine what the network configuration should be. Then I noticed how you had forgotten to disconnect a bunch of circuits, so I freed those up. Finally, I updated the billing records to match the CRM.”
OK, what’s the point of my story? It’s to say that even the toughest integration problems can be solved in step by step fashion. Aligning systems is like solving a jigsaw puzzle where each piece you connect gives you a hint as to what to look for next. You arrive at answers by conducting a series of searches from one system to the next, checking the inconsistencies and reconciling views.
| But aren‘t you relying on an imprecise method of discovering where the errors lie? In a traditional systems integration approach, you’re examining the systems as they were originally designed and conceived. Isn’t that a more logical approach? |
Traditional integration may be the more logical, but it is not the most efficient path -- as the history of telecom integration proves. Integration is often an enormously expensive and risky business.
Consider this: the world’s biggest misaligned data system is not at BT, Verizon, or China Telecom. The world’s biggest misaligned data system is the internet itself. And yet the internet is very effective. People will often examine seven or eight web sites before they decide to buy something. The internet has become a key ordering channel for airlines, hotels, and many other industries, and yet nobody requires a fully integrated and joined view of the internet to get useful work done or to find answers.
The same goes for the systems at telecoms large and small. The point is to deliver as much alignment as is required by the mission, not to align all systems and spend a fortune doing so.
| What are some of the clues you use to connect the dots. How do you how do you achieve accuracy with your system? |
Well the first place to look is field names and id numbers. You try to match these across multiple systems and see what you find. An IP address is a unique identifier within a network. And wherever you have an IP address, it implies the existence of an interface. Likewise, an IP address implies the existence of a router or switch. If an IP address can‘t be associated with a network element, that breaks the “ontology” or rules of existence for things and therefore indicates an error in the data.
Along the way, we can correct a slightly wrong identifier. The whole point is to present the matches the system finds in a way that makes it easy for the network or system expert to make the final classification decisions.
In the area of network reconciliation, we can identify circuits that are likely to be stranded assets. We may not be able to find a match in the network side, but we can investigate services being leased with no associated bill to a customer.
| Other companies, such as Subex, are out there offering network inventory reconciliation solutions to identify stranded assets. How would you distinguish your approach from theirs? |
I know about TrueSource and it’s a fundamentally different methodology. Their starting point involves building a very extensive model of the underlying systems, and then pulling data from those systems so you can look for inconsistencies
Rather than start with a model, Ontology’s approach is to recognize the structure that is implicit in the data systems that people already have. Instead of pulling data from existing systems into another database, we pull it into a graph.
| When you say “graph” I think of a probability graph with a normal distribution curves. Is that what you mean? |
No, I’m using graph in the sense of a map, a fully connected node and edge structure that stores relationships: one entity connects to another entity through this particular relationship. And you can scan the nodes and examine all the relationships, so what you see is a kind of spider web called a “graph”.
What we are really storing is metadata — tags, pointers, and relationships among various databases and objects.
The Ontology Architecture
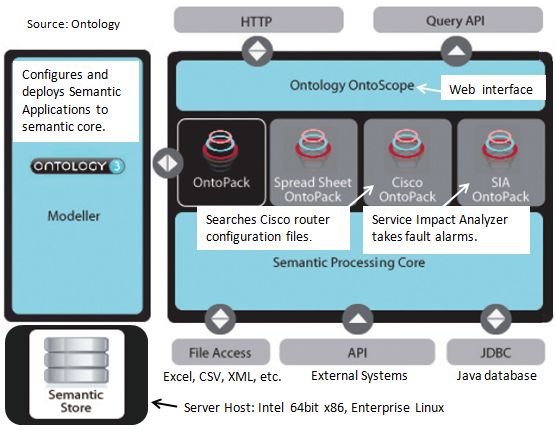
And as we examine the patterns in that graph, we look for consistencies, inconsistencies and when we find them, we classify things. In short, our approach deduces the structure of network and service delivery systems without having to know very much about the kind of data we’re looking at. And using this method we are able to deliver operational value in six to eight weeks, and the reason we can do that is we do not do a big integration at the beginning of the project.
Actually, Leo and I first got the idea for this approach from the intelligence community who pore through massive data sets trying to find terrorist cells. In that scenario, you have no control over where and when the data will change. Investigative work like that is a great example of teasing out the details of underlying systems using a centralized search method.
| Benedict, this is highly interesting stuff. It would be great if you could recap your perspective and value proposition. |
Well, Dan, it’s no secret that the telecom business is getting more complex. New services and new network technology are expanding. In addition, many new partners are entering the scene, be they: virtual network operators, cloud providers, IT outsource partners, over-the-top content providers -- even managed service providers.
But no matter how complex back office systems and partner relationships get, a telecom’s ability to squeeze out greater profits and efficiency depends on knowing a lot about customer behavior and network utilization that only a finer grain level of inter-system analytics can deliver.
So there’s a tremendous need to join data across multiple misaligned systems for business intelligence , optimization, and assurance purposes. But given the nature of today’s business, you need to do that at very low cost. And that tends to rule out those expensive and risky full-scale integration projects that were the norm in the past.
We tackle the problem a different way. We use orchestration and discovery techniques to align systems because they don‘t require you to change out or remodel your existing infrastructure.
What more can I say? Fortunately we became profitable last year and doubled our revenue the last two. So I encourage your readers to check us out.
Copyright 2012 Black Swan Telecom Journal
Black Swan Solution Guides & Papers
- Expanding the Scope of Revenue Assurance Beyond Switch-to-Bill’s Vision — Araxxe — How Araxxe’s end-to-end revenue assurance complements switch-to-bill RA through telescope RA (external and partner data) and microscope RA (high-definition analysis of complex services like bundling and digital services).
- Lanck Telecom FMS: Voice Fraud Management as a Network Service on Demand — Lanck Telecom — A Guide to a new and unique on-demand network service enabling fraud-risky international voice traffic to be monitored (and either alerted or blocked) as that traffic is routed through a wholesaler on its way to its final destinations.
- SHAKEN / STIR Calling Number Verification & Fraud Alerting — iconectiv — SHAKEN/STIR is the telecom industry’s first step toward reviving trust in business telephony — and has recently launched in the U.S. market. This Solution Guide features commentary from technology leaders at iconetiv, a firm heavily involved in the development of SHAKEN.
- Getting Accurate, Up-to-the-Minute Phone Number Porting History & Carrier-of-Record Data to Verify Identity & Mitigate Account Takeovers — iconectiv — Learn about a recently approved risk intelligence service to receive authoritative and real-time notices of numbers being ported and changes to the carrier-of-record for specific telephone numbers.
- The Value of an Authoritative Database of Global Telephone Numbers — iconectiv — Learn about an authoritative database of allocated numbers and special number ranges in every country of the world. The expert explains how this database adds value to any FMS or fraud analyst team.
- The IPRN Database and its Use in IRSF & Wangiri Fraud Control — Yates Fraud Consulting — The IPRN Database is a powerful new tool for helping control IRSF and Wangiri frauds. The pioneer of the category explains the value and use of the IPRN Database in this 14-page Black Swan Solution Guide.
- A Real-Time Cloud Service to Protect the Enterprise PBX from IRSF Fraud — Oculeus — Learn how a new cloud-based solution developed by Oculeus, any enterprise can protect its PBX from IRSF fraud for as little as $5 a month.
- How Regulators can Lead the Fight Against International Bypass Fraud — LATRO Services — As a regulator in a country infected by SIM box fraud, what can you do to improve the situation? A white paper explains the steps you can and should you take — at the national government level — to better protect your country’s tax revenue, quality of communications, and national infrastructure.
- Telecom Identity Fraud 2020: A 36-Expert Analysis Report from TRI — TRI — TRI releases a new research report on telecom identity fraud and security. Black Swan readers can download a free Executive Summary of the Report.
- The 2021 State of Communications-Related Fraud, Identity Theft & Consumer Protection in the USA — iconectiv — This 49-page free Report on communications-related fraud analyzes the FTC’s annual Sentinel consumer fraud statistics and provides a sweeping view of trends and problem areas. It also gives a cross-industry view of the practices and systems that enable fraud control, identity verification, and security in our “zero trust” digital world.
cSwans of a Feather
- GCX Builds a Layer 1 Subsea OSS: Wavelengths to Data Centers & Persistent Edge Connectivity for Clouds — interview with Jim Fagan — A tutorial on the business of undersea cables and how edge computing, clouds, and a subsea software defined network (SDN) will work together to deliver connectivity and advanced IoT use cases such as the connected car.
- How HGC Global Communications Builds Integrated Fiber, Undersea & Platform Solutions for Southeast Asian ISPs & Content Providers — interview with Ravindran Mahalingam — The head of an international telecom division explains the challenges and opportunities faced by content providers, ISPs, gaming firms, and streaming firms. Learn about the market forces at play to win eyeballs in Southeast Asia and why partnering to deliver infrastructure and platform makes sense.
- Multi-Vendor SDN/NFV Services: How Integrators Collaborate to Drive the Next Era of Network Automation — interview with Bartosz Michalik & Marcin Paszkiewicz — What technical steps are required to orchestrate NFV/SDN and legacy multi-vendor networks? This tutorial explains the role of key development standards like OpenDaylight and integration challenges in the new era.
- How to Blaze an Access Path to Siloed Enterprise Data and Avoid the High Cost of Systems Integration — by Dan Baker — Systems integration has always a big issue in the telecom back office. And history tells us that it’s a messy and risky exercise when done on a large scale. But now there’s an alternative to systems integration called “semantic search” and the concept is fully explained in a white paper.
- Clever Integration: The Sherlock Holmes Way to Tease Solutions from a Fog of Misaligned Data — interview with Benedict Enweani — Tired of risky and expensive “big bang” systems integration projects that don‘t solve problems? In this article you’ll learn how deductive reasoning can be used to weave through mountains of tangeled and misaligned data. The approach uses a repeatable method to orchestrate solutions at relatively low cost and can be applied to many B/OSS and assurance problems.
Related Articles
- Tokopedia, Indonesia’s E-Commerce King, Partners with 11 Million Merchants; Adopts Multi-Cloud to Drive Innovation — interview with Warren Aw & Ryan de Melo — Indonesia’s Tokopedia, founded in 2009, has grown to become one of world’s leading e-commerce players. Read about its success, technology direction, and multi-cloud connectivity adoption.
- Bridge Alliance: Knocking Down Regional & Mobile Connectivity Barriers so Connected Car Markets Get Rolling in Asia — interview with Kwee Kchwee — The CEO of an Asian consortium of mobile operators explains how they help simplify and harmonize their members‘ operations in support of multi-national corporations. This integration is enabling two huge industries to come together in Asia: auto manufacturing and telco.
- Epsilon’s Infiny NaaS Platform Brings Global Connection, Agility & Fast Provision for IoT, Clouds & Enterprises in Southeast Asia, China & Beyond — interview with Warren Aw — Network as a Service, powered by Software Defined Networks, are a faster, more agile, and more partner-friendly way of making data global connections. A leading NaaS provider explains the benefits for cloud apps, enterprise IT, and IoT.
- PCCW Global: On Leveraging Global IoT Connectivity to Create Mission Critical Use Cases for Enterprises — interview with Craig Price — A leading wholesale executive explains the business challenges of the current global IoT scene as it spans many spheres: technical, political, marketing, and enterprise customer value creation.
- Senet’s Cloud & Shared Gateways Drive LoRaWAN IoT Adoption for Enterprise Businesses, Smart Cities & Telecoms — interview with Bruce Chatterley — An IoT netowork pioneer explains how LoRaWAN tech fits in the larger IoT ecosystem. He gives use case examples, describes deployment restraints/costs, and shows how partnering, gateway sharing, and flexible deployment options are stimulating growth.
- ARM Data Center Software’s Cloud-Based Network Inventory Links Network, Operations, Billing, Sales & CRM to One Database — interview with Joe McDermott & Frank McDermott — A firm offering a cloud-based network inventory system explains the virtues of: a single underlying database, flexible conversions, task-checking workflow, new software business models, views that identify stranded assets, and connecting to Microsoft’s cloud platform.
- Pure Play NFV: Lessons Learned from Masergy’s Virtual Deployment for a Global Enterprise — interview with Prayson Pate — NFV is just getting off the ground, but one cloud provider to enterprises making a stir in virtual technology waters is Masergy. Here are lessons learned from Masergy’s recent global deployment using a NFV pure play software approach.
- The Digital Enabler: A Charging, Self-Care & Marketing Platform at the Core of the Mobile Business — interview with Jennifer Kyriakakis — The digital enabler is a central platform that ties together charging, self-care, and marketing. The article explains why leading operators consider digital enablers pivotal to their digital strategies.
- Delivering Service Assurance Excellence at a Reduced Operating Cost — interview with Gregg Hara — The great diversity and complexity of today’s networks make service assurance a big challenge. But advances in off-the-shelf software now permit the configuring and visualizing of services across multiple technologies on a modest operating budget.
- Are Cloud-Based Call Centers the Next Hot Product for the SMB Market? — interview with Doron Dovrat — Quality customer service can improve a company’s corporate identity and drive business growth. But many SMBs are priced out of acquiring modern call center technology. This article explains the benefits of affordable and flexible cloud-based call centers.
- Flexing the OSS & Network to Support the Digital Ecosystem — interview with Ken Dilbeck — The need for telecoms to support a broader digital ecosystem requires an enormous change to OSS infrastructures and the way networks are being managed. This interview sheds light on these challenges.
- Crossing the Rubicon: Is it Time for Tier Ones to Move to a Real-Time Analytics BSS? — interview with Andy Tiller — Will tier one operators continue to maintain their quilt works of legacy and adjunct platforms — or will they radically transform their BSS architecture into a new system designed to address the new telecom era? An advocate for radical transformation discusses: real-time analytics, billing for enterprises, partnering mashups, and on-going transformation work at Telenor.
- Paradigm Shift in OSS Software: Network Topology Views via Enterprise-Search — interview with Benedict Enweani — Enterprise-search is a wildly successful technology on the web, yet its influence has not yet rippled to the IT main stream. But now a large Middle Eastern operator has deployed a major service assurance application using enterprise-search. The interview discusses this multi-dimensional topology solution and compares it to traditional network inventory.
- The Multi-Vendor MPLS: Enabling Tier 2 and 3 Telecoms to Offer World-Class Networks to SMBs — interview with Prabhu Ramachandran — MPLS is a networking technology that has caught fire in the last decade. Yet the complexity of MPLS has relegated to being mostly a large carrier solution. Now a developer of a multi-vendor MPLS solutions explains why the next wave of MPLS adoption will come from tier 2/3 carriers supporting SMB customers.
- Enabling Telecoms & Utilities to Adapt to the Winds of Business Change — interview with Kirill Rechter — Billing is in the midst of momentous change. Its value is no longer just around delivering multi-play services or sophisticated rating. In this article you’ll learn how a billing/CRM supplier has adapted to the times by offering deeper value around the larger business issues of its telecom and utility clients.
- Driving Customer Care Results & Cost Savings from Big Data Facts — interview with Brian Jurutka — Mobile broadband and today’s dizzying array of app and network technology present a big challenge to customer care. In fact, care agents have a hard time staying one step ahead of customers who call to report problems. But network analytics comes to the rescue with advanced mobile handset troubleshooting and an ability to put greater intelligence at the fingertips of highly trained reps.
- Hadoop and M2M Meet Device and Network Management Systems — interview with Eric Wegner — Telecom big-data in networks is more than customer experience managment: it’s also about M2M plus network and element management systems. This interview discusses the explosion in machine-to-machine devices, the virtues and drawbacks of Hadoop, and the network impact of shrink-wrapped search.
- The Data Center & Cloud Infrastructure Boom: Is Your Sales/Engineering Team Equipped to Win? — by Dan Baker — The build-out of enterprise clouds and data centers is a golden opportunity for systems integrators, carriers, and cloud providers. But the firms who win this business will have sales and engineering teams who can drive an effective and streamlined requirements-to-design-to-order process. This white paper points to a solution — a collaborative solution designs system — and explains 8 key capabilities of an ideal platform.
- Big Data: Is it Ready for Prime Time in Customer Experience Management? — interview with Thomas Sutter — Customer experience management is one of the most challenging of OSS domains and some suppliers are touting “big data” solutions as the silver bullet for CEM upgrades and consolidation. This interview challenges the readiness of big data soluions to tackle OSS issues and deliver the cost savings. The article also provides advice on managing technology risks, software vendor partnering, and the strategies of different OSS suppliers.
- Calculated Risk: The Race to Deliver the Next Generation of LTE Service Management — interview with Edoardo Rizzi — LTE and the emerging heterogeneous networks are likely to shake up the service management and customer experience management worlds. Learn about the many new network management challenges LTE presents, and how a small OSS software firm aims to beat the big established players to market with a bold new technology and strategy.
- Decom Dilemma: Why Tearing Down Networks is Often Harder than Deploying Them — interview with Dan Hays — For every new 4G LTE and IP-based infrastructure deployed, there typically a legacy network that’s been rendered obsolete and needs to be decommissioned. This article takes you through the many complexities of network decom, such as facilities planning, site lease terminations, green-safe equipment disposal, and tax relief programs.
- Migration Success or Migraine Headache: Why Upfront Planning is Key to Network Decom — interview with Ron Angner — Shutting down old networks and migrating customers to new ones is among the most challenging activities a network operators does today. This article provides advice on the many network issues surrounding migration and decommissioning. Topics discussed include inventory reconciliation, LEC/CLEC coordination, and protection of customers in the midst of projects that require great program management skills.
- Navigating the Telecom Solutions Wilderness: Advice from Some Veteran Mountaineers — interview with Al Brisard — Telecom solutions vendors struggle mightily to position their solutions and figure out what to offer next in a market where there’s considerable product and service crossover. In this article, a veteran order management specialist firm lays out its strategy for mixing deep-bench functional expertise with process consulting, analytics, and custom API development.
- Will Telecoms Sink Under the Weight of their Bloated and Out-of-Control Product Stacks? — interview with Simon Muderack — Telecoms pay daily for their lack of product integration as they constantly reinvent product wheels, lose customer intelligence, and waste time/money. This article makes the case of an enterprise product catalog. Drawing on central catalog cases at a few Tier 1 operators, the article explains the benefits: reducing billing and provisioning costs, promoting product reuse, and smoothing operations.
- Virtual Operator Life: Enabling Multi-Level Resellers Through an Active Product Catalog — interview with Rob Hill — The value of product distribution via virtual operators is immense. They enable a carrier to sell to markets it cannot profitably serve directly. Yet the need for greater reseller flexibility in the bundling and pricing of increasingly complex IP and cloud services is now a major channel barrier. This article explains what’s behind an innovative product catalog solution that doubles as a service creation environment for resellers in multiple tiers.
- Telecom Blocking & Tackling: Executing the Fundamentals of the Order-to-Bill Process — interview with Ron Angner — Just as football teams need to be good at the basics of blocking and tackling, telecoms need to excel at their own fundamental skillset: the order-to-cash process. In this article, a leading consulting firm explains its methodology for taking operators on the path towards order-to-cash excellence. Issues discussed include: provisioning intervals; standardization and simplicity; the transition from legacy to improved process; and the major role that industry metrics play.
- Wireline Act IV, Scene II: Packaging Network & SaaS Services Together to Serve SMBs — by John Frame — As revenue from telephony services has steadily declined, fixed network operators have scrambled to support VoIP, enhanced IP services, and now cloud applications. This shift has also brought challenges to the provisioning software vendors who support the operators. In this interview, a leading supplier explains how it’s transforming from plain ol‘ OSS software provider to packager of on-net and SaaS solutions from an array of third party cloud providers.
- Telecom Merger Juggling Act: How to Convert the Back Office and Keep Customers and Investors Happy at the Same Time — interview with Curtis Mills — Billing and OSS conversions as the result of a merger are a risky activity as evidenced by famous cases at Fairpoint and Hawaiian Telcom. This article offers advice on how to head off problems by monitoring key operations checkpoints, asking the right questions, and leading with a proven conversion methodology.
- Is Order Management a Provisioning System or Your Best Salesperson? — by John Konczal — Order management as a differentiator is a very new concept to many CSP people, but it’s become a very real sales booster in many industries. Using electronics retailer BestBuy as an example, the article points to several innovations that can — and are — being applied by CSPs today. The article concludes with 8 key questions an operator should ask to measure advanced order management progress.
- NEC Takes the Telecom Cloud from PowerPoint to Live Customers — interview with Shinya Kukita — In the cloud computing world, it’s a long road from technology success to telecom busness opportunity. But this story about how NEC and Telefonica are partnering to offer cloud services to small and medium enterprises shows the experience of early cloud adoption. Issues discussed in the article include: customer types, cloud application varieties, geographic region acceptance, and selling challenges.
- Billing As Enabler for the Next Killer Business Model — interview with Scott Swartz — Facebook, cloud services, and Google Ads are examples of innovative business models that demand unique or non-standard billing techniques. The article shows how flexible, change-on-the-fly, and metadata-driven billing architectures are enabling CSPs to offer truly ground breaking services.
- Real-Time Provisioning of SIM Cards: A Boon to GSM Operators — interview with Simo Isomaki — Software-controlled SIM card configuration is revolutionizing the activation of GSM phones. The article explains how dynamic SIM management decouples the selection of numbers/services and delivers new opportunities to market during the customer acquisition and intial provisoining phase.
- A Cynic Converted: IN/Prepaid Platforms Are Now Pretty Cool — interview with Grant Lenahan — Service delivery platforms born in the IN era are often painted as inflexible and expensive to maintain. Learn how modern SDPs with protocol mediation, high availability, and flexible Service Creation Environments are delivering value for operators such as Brazil’s Oi.
- Achieving Revenue Maximization in the Telecom Contact Center — interview with Robert Lamb — Optimizing the contact center offers one of the greatest returns on investment for a CSP. The director of AT&T’s contact center services business explains how telecoms can strike an “artful balance” between contact center investment and cost savings. The discussion draws from AT&T’s consulting with world class customers like Ford, Dell, Discover Financial, DISH Network, and General Motors.
- Mobile Broadband: The Customer Service Assurance Challenge — interview with Michele Campriani — iPhone and Android traffic is surging but operators struggle with network congestion and dropping ARPUs. The answer? Direct resources and service quality measures to ensure VIPs are indeed getting the quality they expect. Using real-life examples that cut to the chase of technical complexities, this article explains the chief causes of service quality degradation and describes efficient ways to deal with the problem.
- Telco-in-a-Box: Are Telecoms Back in the B/OSS Business? — interview with Jim Dunlap — Most telecoms have long since folded their merchant B/OSS software/services businesses. But now Cycle30, a subsidiary of Alaskan operator GCI, is offering a order-to-cash managed service for other operators and utilities. The article discusses the company’s unique business model and contrasts it with billing service bureau and licensed software approaches.
- Bricks, Mortar & Well-Trained Reps Make a Comeback in Customer Management — interview with Scott Kohlman — Greater industry competition, service complexity, and employee turnover have raised the bar in the customer support. Indeed, complex services are putting an emphasis on quality care interactions in the store, on the web, and through the call center. In this article you’ll learn about innovations in CRM, multi-tabbed agent portals, call center agent training, customer treatment philosophies, and the impact of self-service.
- 21st Century Order Management: The Cross-Channel Sales Conversation — by John Konczal — Selling a mobile service is generally not a one-and-done transaction. It often involves several interactions — across the web, call center, store, and even kiosks. This article explains the power of a “cross-channel hub” which sits above all sales channels, interacts with them all, and allows a CSP to keep the sales conversation moving forward seamlessly.
- Building a B/OSS Business Through Common Sense Customer Service — by David West — Delivering customer service excellence doesn‘t require mastering some secret technique. The premise of this article is that plain dealing with customers and employees is all that’s needed for a winning formula. The argument is spelling out in a simple 4 step methodology along with some practical examples.


